Levelling up?
I’ve spent 13 years now interested in Open Badges and, more recently, Verifiable Credentials.* When you explain something over and over again you get better at explaining it. You also start to notice patterns. This post is about one of those patterns.
* Happily, v3.0 of the Open Badges specification uses the Verifiable Credentials data model. Find out more.

In broad brushstrokes, credentials are awarded in a similar way within academic systems. Define something worth learning, build a curriculum and scheme of work, then design some learning activities. Create an assessment based on the learning activities, and then issue credentials based on the outcome of the activities.
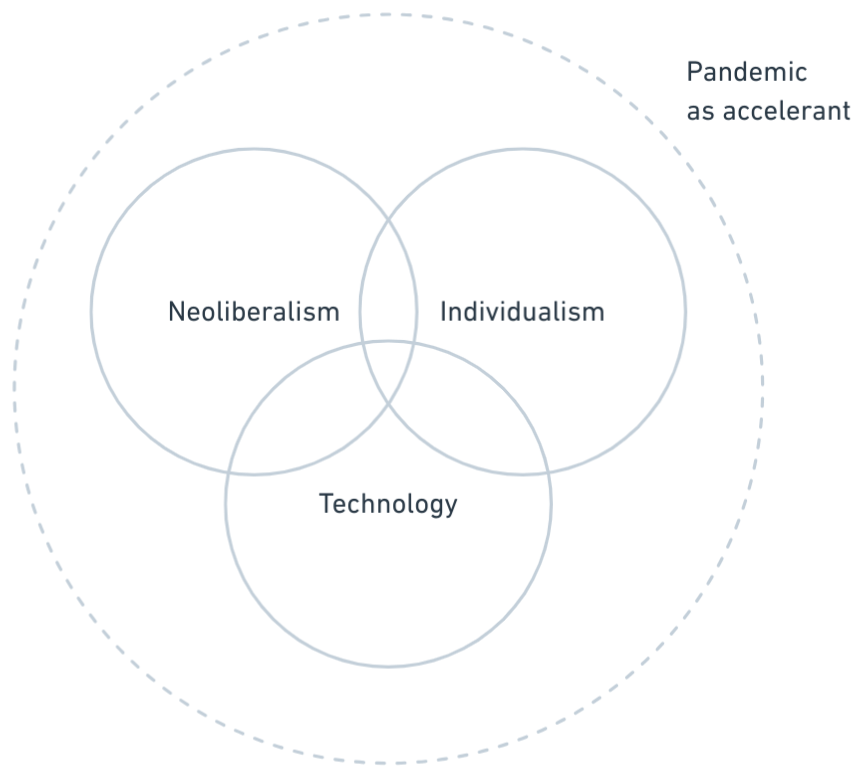
We’re so used to this that we forget that this is very far removed from how the world actually works. Learning outside of the classroom is messy, episodic, and relational. So how do we go about capturing this?
A common mental model I’ve seen is using gold, silver, and bronze as ‘tiers’ within a badging system. However, without a background in assessment design, these tiers often become even more arbitrary than those in formal education. There’s often a huge ask even to get on the bottom rung of the ladder. Why? I’d just give people badges for turning up. They’re free! You can issue as many as you like.
At Mozilla, where I also served as Web Literacy Lead, we aimed to link the Web Literacy Map to badges, and initially considered levels. However, we quickly realised that doing this globally in a decentralised way is essentially impossible. Instead, mapping badges to skills in specific areas made much more sense. Context matters: what might be ‘advanced’ in one place could be ‘beginner’ elsewhere.
Instead, mapping badges related to skills in a particular area made much more sense. Context does, after all, matter: what might be seen as ‘advanced’ somewhere might be seen as ‘beginner’ elsewhere, and vice-versa. Badges for levels are all well and good, but those levels need to describe something worthwhile.
After leaving Mozilla, I spent all my consultancy time with City & Guilds , collaborating extensively with Bryan Mathers (who created the images in this post). Even as an awarding body, it took City & Guilds staff a while to grasp all the possibilities badges offered.
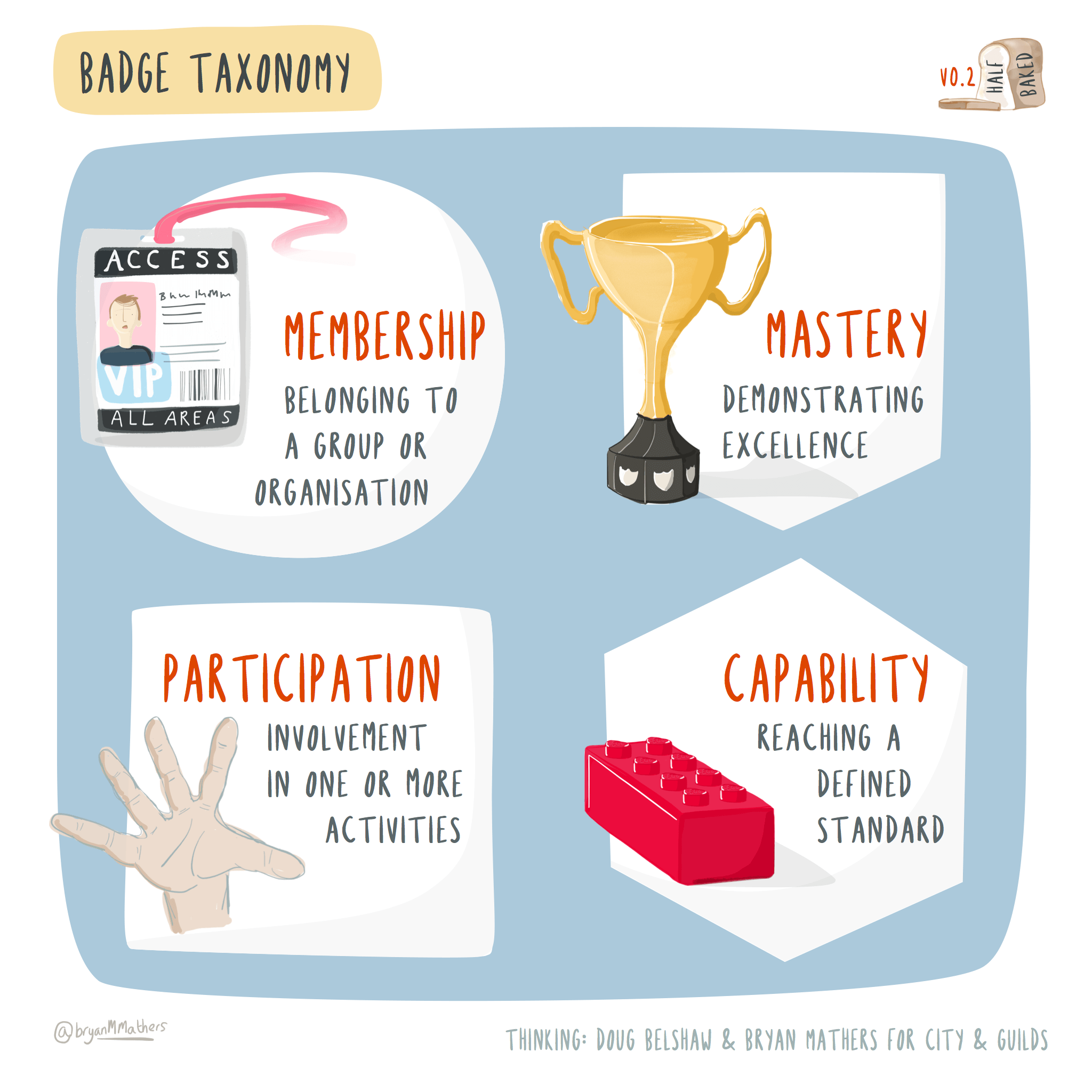
Bryan created this super-simple taxonomy from our conversations as a conversation starter with City & Guilds staff, helping them realise that recognition in the form of participation in something, or membership of a thing, was just as legitimate as reaching a defined standard or demonstrating excellence. Badges help us tell a story about the learning journey we’ve been on.
For me, this has been one of the main takeaways from my own learning journey with Open Badges so far: when you’ve got enough verified ways of showing what you’ve done, levels don’t matter that much. We’re all different, so recognising and celebrating that is, to me, more important than expecting everyone to fit into pre-defined boxes.
So if you’re designing assessments based on academic research for something that’s high stakes then, by all means, design a rigorous system. For everything else, treat it like a product: figure out how your users (the people to be badged) want to be recognised, design around that, and iterate.
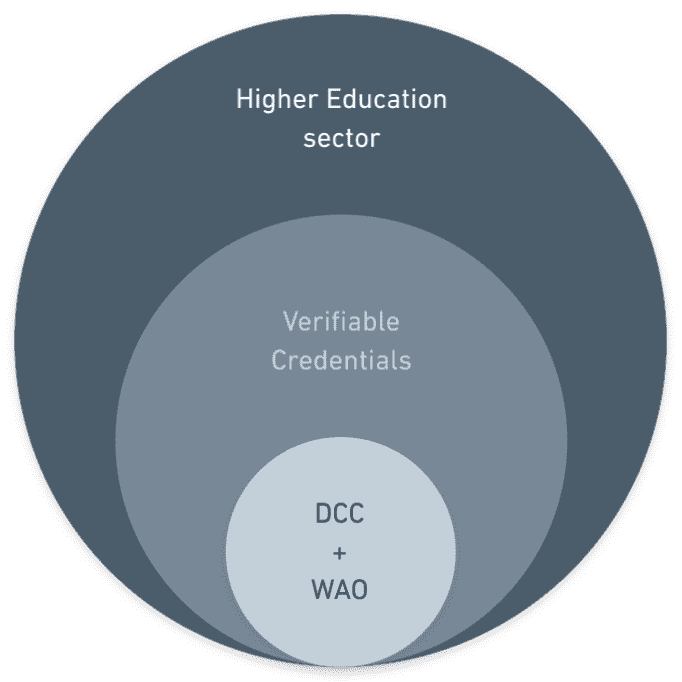
If you’re curious in how to go beyond the ‘microcredential’ approach to digital credentials, you might be interested in the free WAO email-based course Reframing Recognition. You’re also welcome to join us as part of the Open Recognition is for Everybody community.